Whether you read this headline and thought “Extra programs are annoying”, or “Yep, some programs are extra annoying”, it doesn’t matter. Both are equally true.
Annoying programs come in all shapes and sizes. Some are free, some are not, and some are free for a certain number of days. These free trials are known as Bloatware. Like Microsoft Office, they come pre-installed on your new computer or mobile device. You pretty much have no choice with these. The only thing you can do is decide which ones to keep (i.e. eventually buy), and which ones to delete.
Where you do have a choice are with programs I like to call tag-alongs. They’re officially known in the tech industry as adware, spyware, junkware, or crapware… and those are only the names I can reference in polite society. These names alone should tell you what the IT World thinks of them.
Grab a cup of tea and let me tell you about tag-alongs.
 Once upon a time in computing history, a business decided when a person downloaded a chosen program it’d be profitable to add theirs as a bonus. The end-user thought receiving extra stuff for nothing was wonderful until he downloaded four more programs and was extended a dividend of four more tag-along programs. He realized some blessing were really curses in disguise, just like King Midas.
Once upon a time in computing history, a business decided when a person downloaded a chosen program it’d be profitable to add theirs as a bonus. The end-user thought receiving extra stuff for nothing was wonderful until he downloaded four more programs and was extended a dividend of four more tag-along programs. He realized some blessing were really curses in disguise, just like King Midas.
Unfortunately, there isn’t a happy ending… yet. But I’m going to help you recognize where these tag-alongs come from, and how to avoid them.
Most tag-along programs come with free downloads. I won’t say all tag-alongs come with freebies for the same reason a person shouldn’t say “never” or “always”.
In our story, we don’t care what causes those pesky additional programs to attack our computer, we just care that they do.
Why Are Tag-along Programs Bad?
- They slow down your browser.
Ever wonder how the Internet knows the exact brand of something you’ve just purchased? Tag-along programs. Stealth programs known as Spyware or Adware sit in the back of your computer watching your purchases and website visits. Later they automatically toss-up advertisements that might interest you.
Why is this bad? These programs take precious seconds off your download speeds and clog up your computer’s RAM and hard drive memory.
Yes, we’re only talking extra seconds added, but  compound this by several programs and your computer speeds may rival 56K dial-up modems. Remember dial-up? I really don’t either. Trust me, it was horribly slow; we just didn’t realize it at the time.
compound this by several programs and your computer speeds may rival 56K dial-up modems. Remember dial-up? I really don’t either. Trust me, it was horribly slow; we just didn’t realize it at the time.
- They load too many toolbars.
PC Magazine posted a super example of what happens when bonus toolbars load along with other programs. See the bottom where it says PC? That’s the PC Magazine website… under all the toolbars.

- They take up memory.
Programs are programs. People think a few extra megabytes of RAM or storage space used has no impact. It does.
It’ll help us understand by knowing how computer memory works.
How Hard Drive Memory is Used
Imagine your computer hard drive as a piece of graph paper. There are squares across plus up and down where we save data. The top left square gets the first item saved. We’ll pretend each square stores a byte of data.
First, I save a word processing document worth ten squares (bytes). Then I find a picture of the Mona Lisa I like so I’m saving it. Mona’s cost in space is five squares. So far I’ve saved fifteen squares of total data.
Oh, I forgot. I need to edit down my document; it’s too long. I erase two squares of data and re-save. I now have two open squares between my document and Mona on my hard drive.
Now I create a spreadsheet worth seven squares. Data saves in all open squares first. This means two squares of spreadsheet data are saved between my document and Mona while the last five of the seven squares save behind Mona.
This happens over and over as we save items to our hard drives. Computers slow down when we ask them to piece together an item spread out over many squares. NOTE: To speed up your computer, you can defragment or defrag your hard drive. You’ve heard that before, haven’t you? See. You’re smart.
What is RAM Memory?
Think of RAM memory like a kitchen counter. I store my food (data) in a refrigerator (hard drive), but when I want to use it I need a place to set it while I cook (RAM memory). Computer items (documents/internet pages/pictures park in RAM memory as I edit/read/view them. The larger the countertop (Random Access Memory), the more food (data) I can have out at one time.
Spotting Tag-along Programs
Let’s talk about spotting rogue programs that seek us out. They sneak into our computers when we’re on auto-pilot after a long day, or after a frustrating hour trying to find a usable download.
- Make sure to download the correct program.
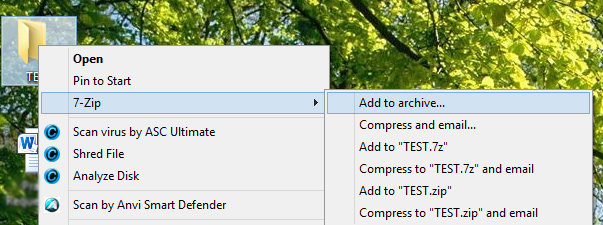
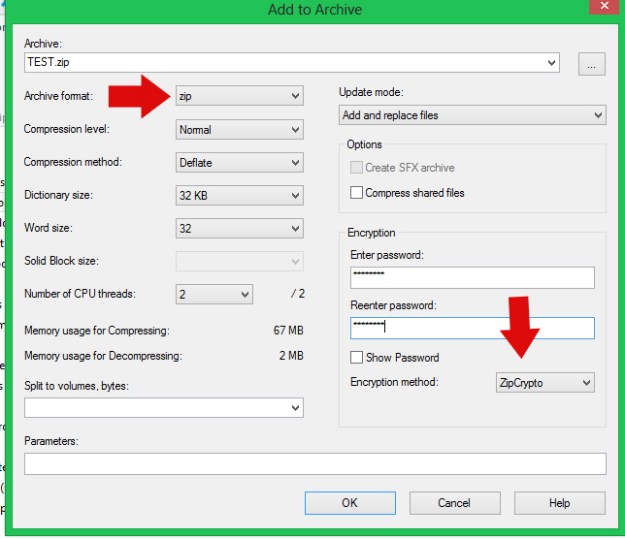
This is the download screen I posted a few weeks ago in Password Protecting Items in Windows 8.
Even a trusted site like Download.com can be confusing. I wanted the 7-Zip download. There are at least two other programs on this page vying for my download. Neither of which I want.
- Uncheck all boxes that will cause you to say, “Huh? How’d that get there?” later.
This is Java. You know Java. Almost every computer in the world runs something that uses Java. Well, when you update your Java — don’t worry, it’ll remind you — you’ll see this.
If you don’t uncheck the boxes, not only will you download and install the Ask search app, you’ll make it your default browser and your homepage. Don’t do it.
- Uncheck the boxes unless you really want the toolbar. You probably don’t if you’ve been fine searching the World Wide Web up to now.

There. Don’t you feel better? Now you know what to look for to avoid downloading adware, spyware, junkware, and crapware.
What? You think you’re already are infected? Don’t worry. You can get rid of those with no needles involved.
I can’t do better in my explanations than to direct you to Kim Komando’s site. She has easily understandable instructions. Thanks, Kim.
Remove Unwanted Toolbars-Kim Komando
Have a wonderful week, and thanks again for following Patti’s Pathways. Y’all come back now, ya’ hear? 😀
DISCLAIMER: Any and all ideas presented in this blog are solely my own unless otherwise noted. I experience troubles with technology just like any other person, and if I stumble upon a fix or suggestion I feel could benefit others I pass it along. At no time, have I suggested or implied that I hold any degrees or certificates related to computer repair.
I have during my career assembled parts into working computers; done troubleshooting on hardware and software; utilized a great many computer programs and software; designed and updated websites and blogs; as well as created brochures, banners, and flyers.