 Welcome 2015 with a Faster, Cleaner, More Cooperative Computer
Welcome 2015 with a Faster, Cleaner, More Cooperative Computer
I don’t mean with a new computer, but if you got one for Christmas… Booya! to you. I’m talking about cleaning the crapware and extra programs from your good old ancient PC or laptop hard drive. It’ll run faster and better. Trust me. You’ll like it.
Between computer geeks I know and online gurus, I’ve got a few great suggestions for programs that take the work out of computer clean up.
Did I mention all of the programs use free software? If you’re impressed with the freebie, you can always upgrade to get more features. If you aren’t, it’s easy—and cheap—to remove and try something different.
 DISCLAIMER: I have zero tech budget that isn’t from my own pocketbook. No software company has asked me to promote their programs.
DISCLAIMER: I have zero tech budget that isn’t from my own pocketbook. No software company has asked me to promote their programs.
CLEANING YOUR PC
First stop on our tour is our old friend Download.com. Remember it? No, Well, it’s your one-stop shopping headquarters for free and paid program downloads. Plus it offers editor and user reviews for all downloads. I find it super helpful to know what other people think of a product before I commit it to my hard drive, even free ones.
I’ll add direct links for most programs I’m suggesting, but download.com is a great place to find info about any program you want to check out.
Here’s a link to http://www.download.com, but for future reference when you search, it’ll look like this: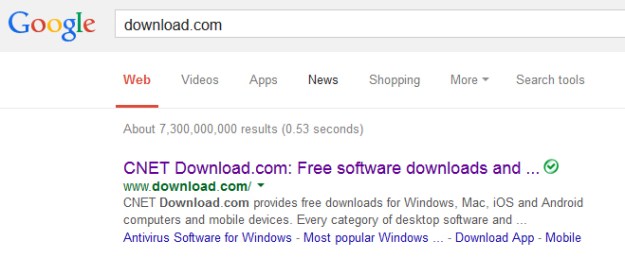
NOTE ONE: the above link takes you to the Windows page. There are tabs across the top so you can search Mac, iOS, or Android applications as well.
NOTE TWO: It’s best to remove a program you don’t use or aren’t thrilled with rather than download a new one and leave them both on your harddrive. Some programs, like wayward children, don’t play well with others. I’ll tell you more about removing programs later in this blog.
ABOUT DOWNLOAD.COM: While it doesn’t covertly add extra programs you don’t want, it does have paid advertisers. Be aware of where your download is versus paid ad downloads.

Beginner Computer Users and Beyond
Beginning computer users, this section is for you.
These programs do the work for you and you don’t have to worry that they’ll erase something they shouldn’t.
FYI: Some programs require a bit of software knowledge to use effectively (i.e. knowing which programs to keep thus not turning your computer into an expensive doorstop).
The “Beyond” in the title means these programs are equally useful for seasoned computer users, including programmers.
Must-Have Programs:
1) CCleaner
CCleaner is a program by Piriform. It cleans unused and temporary files from your hard drive, cleans your browser history, and more. You can tweak it to clean, or not, any areas you wish.
I’ve used it for years and it’s never erased files necessary to run my computer. It’s not set to find those. Try it.
Download it here: CCleaner
 2) Advanced System Care
2) Advanced System Care
This is my current computer protection system. I say system because Advanced System Care does it all: anti-virus, system security, system optimization and clean up, even blocks malicious data stealing programs. It scans, repairs and optimizes. And that’s the free one. Upgrading to the Pro versions is very reasonable.
Get it here: Advanced System Care
 3) Malware Bytes
3) Malware Bytes
For removal of malicious and simply annoying programs infiltrating your computer, this is it. The free version won’t protect your computer from attack, but it’s great for removing Trojans and other hurtful viruses or adware.
Download it here: Malware Bytes
The above group of programs will clean and secure your computer causing it to run faster and safer. It’s well worth the effort.
NOTE: If you leave a cleaning program set to clear your browser cookies, it will most likely also remove your saved passwords and I.D.’s, unless a specific option is chosen to leave these alone. But…i t’s not always a bad thing to clean I.D.’s out of your computer’s memory banks.
FYI: I never save passwords unless I don’t care if the site gets hacked.
 Intermediate Computer Users and Beyond
Intermediate Computer Users and Beyond
There are really good programs out there that take a bit of knowledge, patience (to research what to get rid of), or both to use. HiJack This is one of these.
1) Hijack This
This program is owned by Trend Micro, and can nose out viruses and Trojans with the best of them. Like Malware Bytes, it’s a removal tool.
With Hijack This, you’ll need to know your programs. It will remove indescriminantly… which is bad if it deletes programs needed to run your computer.
You can find it here: Hijack This
NOTE FOR BEGINNERS: You can use these types of programs, but don’t let them blanket delete anything. They’re set to scan everything, and don’t descriminate between harmful and helpful programs.
TIP: If you don’t know what something installed on your computer does, err on the side of caution and leave it alone. A google search will usually tell you about a program, file, registry entry, etc. you’re thinking of deleting, and if you should or not.
 Most removal tools allow you to quarantine files and this is super.
Most removal tools allow you to quarantine files and this is super.
Why? Sometimes viruses disguise themselves as system files. When you quarantine a file, it’s not removed from your computer. Rather it’s stuck away in “file jail”. If you find your computer runs fine with it in jail, it was a virus and not a system file so it’s safe to permanently empty your quarantine folder.
Other Programs I’ve Used:
Windows Defender: Don’t forget about this one. It’s a nice little protective program that comes with your copy of Windows and is enabled by default.
Avast Anti-Virus: I really liked Avast when I used it. I’m not using it currently. It can be set to detect threats, but a few things sneak in anyway.
AVG Anti-Virus: For detection and removal it’s not as good as Malware Bytes, but it’s great at protecting against spyware.
Ad-Aware Anti-Virus: (by Lavasoft): I liked Ad-Aware. It didn’t find as many problems as Malware Bytes, but it did a good job.
Spybot Malware Remover: I haven’t found anything with Spybot that Malware Bytes did’t detect, but it’s a great little program.
Comodo Anti-Virus: I wasn’t as psyched about Comodo as some techies because it evolves like artificial intelligence as it learns your computing habits. You tell it which sites and programs you want to allow each time you visit a site or install a program.
Part of my problem was when I tried Comodo I had Windows Vista as an OS. Each time I reinstalled Vista (which was often), I had to start over training Comodo. It got old fast. But you might like it. If you don’t, it’s easily removed.
Anvi Ad-Blocker: I’m currently using this. As far as I can tell, It works very well. If you wish to try it, you can find it here: Anvi Ad-Blocker
TIP: I love the notification area (that’s its name) at the bottom right of my Windows Desktop. I house all my mainentance and cleanup icons there plus a lot more.

 And yeah, that’s the actual temperature outside where I live… in Fahrenheit.
And yeah, that’s the actual temperature outside where I live… in Fahrenheit.
And no, I don’t live in Alaska, but sometimes the lower forty-eight are colder.
Now that we’ve talked about programs to add to your cleaning arsenal, let’s talk about removing programs you don’t want to free up memory.
Removing Unwanted Programs
Removing programs is done through your Control Panel. Remember how to access that? No? Here’s a refresher then.
In Windows 7 and before, 1) open the start menu in the corner of your taskbar. 2) click Control Panel.

In Windows 8 and 8.1, 1) go to Settings at the bottom of your Charms Bar (hover over the top or bottom right corners of your screen to open it), and 2) Choose Control Panel.

In Windows 10, no clue. What? You didn’t know there was a Windows 10. Find out more about it at Welcome Windows 10!
3) In Control Panel, you have a plethora — yes, a plethora — of choices. Find the one labeled 4) Programs and Features and click on it.
Oops, don’t see it? You’re in Catagory View. Change the view to Large Icons so you have an alphabetical listing. So much easier.
Under Programs and Features, you’ll see all the individual programs you can or want to uninstall. Find any programs you currently aren’t using or don’t want, and uninstall.
TIP: If you aren’t sure what a program does, google it. I recently uninstalled my weather app — yep, the same one that says it’s 3 degrees Fahrenheit outside — by mistake. It was no biggy, but it’ll save time if you know what programs run your features.
RECAP OF COMPUTER CLEAN UP
These can be done in any order. Remember defrag and full scans take awhile, while cleaning old unused shortcuts, browser history and things with CCleaner takes less time.
1) Run CCleaner and remove the extra junk it finds.
2) Scan and enable protections with Advanced System Care.
3) Run Malware Bytes and remove extra malware it locates.
4) Uninstall from Programs and Features unused or unwanted programs.
5) Lastly, it’s time to defragment your hard drive memory.
Knowing how hard drives use memory will help you understand why defragging a hard drive speeds up your computer.
From Spotting Extra Annoying Programs:
How Hard Drive Memory is Used
Imagine your computer hard drive as a piece of graph paper. There are squares across plus up and down where we save data. The top left square gets the first item saved. We’ll pretend each square stores a byte of data.
First, I save a word processing document worth ten squares (bytes). Now I’ve found a picture of the Mona Lisa I like so I’m saving it. Mona’s cost in space is five squares. So far I’ve saved fifteen squares of total data.
Oh, I forgot. I need to edit down my document; it’s too long. I erase two squares of data and re-save. I now have two open squares between my document and Mona on my hard drive.
Now I create a spreadsheet worth seven squares. Data saves in all open squares first. This means two squares of spreadsheet data are saved between my document and Mona while the last five of the seven squares save behind Mona.
This happens over and over as we save items to our hard drives. Computers slow down when we ask them to piece together an item spread out over many squares.
Defragging Your Hard Drive
In Windows 7 or before, open the Disk Defragmenter by choosing Start > All Programs > Accessories > System Tools > Disk Defragmenter.
In Windows 8, the name’s been changed to Optimize Drives.

FYI: Obit (Advanced System Care) has a Smart Defrag program that does the same thing.
 After you’ve tried the things I’ve suggested above, you should be pleased with how well your computer works.
After you’ve tried the things I’ve suggested above, you should be pleased with how well your computer works.
Have a Happy New Year’s and a very productive 2015. And thanks again for following Patti’s Pathways. 😀
DISCLAIMER: Any and all ideas presented in this blog are solely my own unless otherwise noted. I experience troubles with technology just like any other person, and if I stumble upon a fix or suggestion I feel could benefit others I pass it along. At no time, have I suggested or implied that I hold any degrees or certificates related to computer repair.
I have during my career assembled parts into working computers; done troubleshooting on hardware and software; utilized a great many computer programs and software; designed and updated websites and blogs; as well as created brochures, banners, and flyers.

















